Introduction
Proton Authenticator : Version 1.1.1 (Latest Software). In an era when digital privacy and cybersecurity concerns rank as the most critical issues, managing an individual or an organization’s internet-facing identity is now imperative. This is where two-factor authentication (2FA) rules; it is the best means to keep strangers from having access to accounts.

In order to make this feature hassle-free, secure, and privacy-protective, Proton Authenticator 1.1.1 provides a trustworthy solution by the same developers who created ProtonMail and the Switzerland-headquartered company that is widely known for its dedication to internet security and data privacy.
Proton Authenticator compromises the idea of creating a secure and cloud-independent way of generating 2FA codes without synchronization to untrusted cloud services that can harm user privacy. Proton Authenticator has been designed with utmost transparency, privacy, and security in fans. It puts users in full control of their public and private keys, presenting a condition where no sensitive data will be able to leave their devices.
The program includes files that add to the mobile version with their capabilities, such as management for professional and secure users who want to manage their keycards by desktop systems.
You May Also Like :: QFX KeyScrambler Professional : Version 3.18.0.5 (Latest Software)
Description
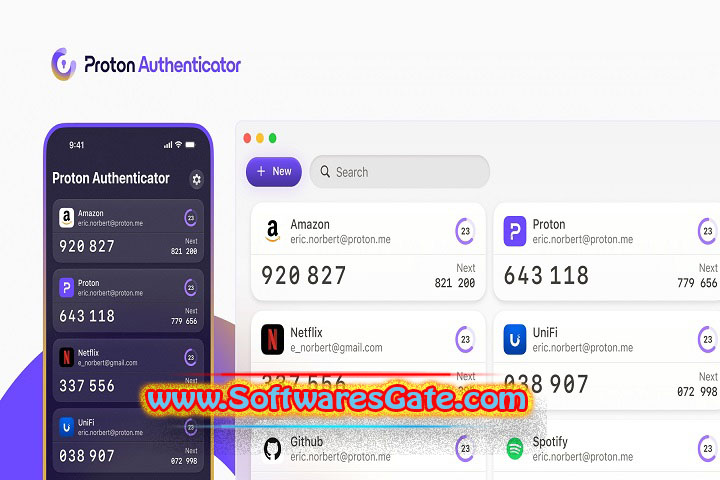
Proton Authenticator 1.1.1 encompasses a brand-new version of a desktop program for secure management of time-based onetime passwords (TOTPs) and multiple authentication accounts at the same time. This could be used as a separate universal 2FA tool that offers 2FA compatibility for many services: Google, Microsoft, GitHub, Facebook, Twitter, and so on. It kills the reliance on mobile-only authenticators, which gives a better desktop experience that is still safe and secure.
What sets Proton Authenticator apart from other tools that are available out there is that it has zero-knowledge encryption, everything is open-source, and there is a strong stand towards this philosophy. Each key is contained in a separate file, and the keys are encrypted on your local machine.
Being one of the few authenticators that doesn’t sync data through cloud accounts, if a user’s service is any less than inspired, you can trust that you will always remain the sole owner of your secrets. The issue resolves into an unusually strong system of authentication that dovetails beautifully with other secure products from Proton.
The new version 1.1.1 boasts (omit)better performance, newer and compact Windows 10 and 11 compatibility, and further improves synchronization features among various Proton services. It also delivers enhanced backup and export options, which let users better store and transfer their 2FA tokens securely across devices.
Overview
Proton Authenticator presents a clear and trustworthy process (omit), which can make all your authentication code administration from a single reliable centralized spot. It incorporates both Time-based OneTime Password (TOTP) and HMAC-based Onetime Password (HOTP) technologies, the same as the ones in Google Authenticator and Auty, which makes it nearly universally applicable via any service that has to authorize through 2FA.
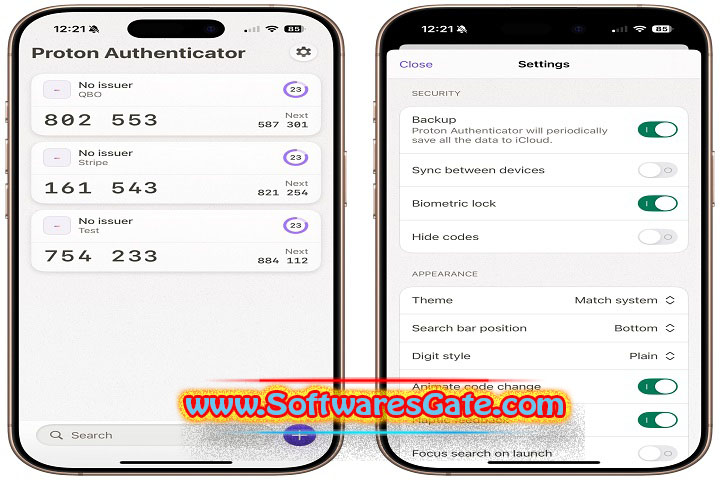
The split and simple interface of Proton Authenticator is appealing. It makes managing numerous authentication tokens feel comfortable and controlled. The details of each account highlight the site name that is being authenticated at, and the maintenance of privacy is guaranteed since the code is automatically changed in a 30-second cycle. This application allows users to copy data items to their clipboard for quick opening of any page, or scan QR codes to add new items to the list directly from the desktop.
With the latest version 1.1.1, we have also taken the security to the next level by allowing the services to be in perfect synchronization and better exports/imports that pave the way for easy data management. The software still has the option of password protection for the main vault. Unauthorized personnel are likely to be locked out whenever the system is locked or shut down on shared systems.
On the whole, Proton Authenticator sums up a great compromise in linking usability and privacy, namely no ads, no trackers, no sneaky spyware lurking beneath the scenes. In the short term, it feels like security magic that rubs off the shoulders of the weary.
You May Also Like :: Phoenix Customizer : Version 1.1.9 (Latest Software)
Software Features
Open-source and audited security
Proton Authenticator, behaving with the open-source model, provides its source code publicly for both commercial and non-commercial purposes. Therefore, with the open-source software, it is possible to view the software code structure and perform a thorough audit; the necessity of it goes without saying. Openness makes it possible to build trust and security, which safeguards the applications against possible bugs and data leakages.
Local Encryption
Each Atlas user is a guardian of his or her own data assets. The data travels no further than your laptop. The only way data could be hacked is if it can not be hacked.
Cross-Platform Compatibility
This program is suitable for all your devices – desktop (Windows, macOS, Linux). And mobile (Android, iOS) – without any issues. The main version (PC) guarantees you fast and stable work.
Supports Multiple Accounts
Unlimited 2FA tokens are here to add to your collection. Just don’t forget your media accounts, networking, work or player’s tools and monitor them all from the same single place.
QR Code Scanning and Manual Entry
In order the account in the new service. It’s enough to scan a QR code with the help of your laptop camera. But you can also type the secret manually where the camera does not work.
Time-Based and HMAC-Based OTP Support
Supports the two methods TOTP and HOTP. It is fully verified that all web and service sites that use two-phase verification will continue their granted convenience.
Software Features
Password-Protected Vault
Users can add an extra layer of defense by setting the main application with their master password.
Backup and Restore Functionality
We ensure your backup and restore functionality offers enough backup. And the import of 2FA keys so that you can create crypto-secure backups. And also use them for a safe recovery if your system reinstallations are required.
User-Friendly Interface
Minimalistic yet efficient UI design. The 1.1.1 version carries on visual improvements in this general direction with better navigation and code readability.
Offline Operation
Restore a full system, work completely offline: don’t be dependent on an Internet connection to satisfy your needs even in case of network break-ins.

No Tracking or Ads
Just like other tools in the Proton Software series. The Authenticator tool does not contain any ads. Proton services have a very strict privacy ethics system, furthermore. Therefore, your phone won’t be tracking your navigation in the background.
Automatic Code Refresh
The generating tokens refresh automatically every 30 seconds. Such waving the concern about the traditional authenticator after every. This assists in the stable and in good time code generation.
You May Also Like :: Intelligent Editing PerfectIt Pro : Version 6.4.0 (Latest Software)
How to Install?
Download the Installer:
You can download Windows Proton Authenticator 1.1.1 on the official Proton or through the GitHub repository. All the installers are free.
Run the Installer:
Run the setup file, pointing a browser to the download directory with a a double-click. It will launch a window asking you to go through the steps of installation. Click the “install” button in any dialog that pops up.
Launch the Application:
Find the Proton Authenticator icon on the computer screen. Or go to “Start” and then run the program.
Set Up a Master Password (Optional):
A vault password has been pre-configured; you may choose to configure your master password. If one is not one.
Add Accounts:
Scan the code under “Add Account” and enter the generated authentication secret on the website. Or application you wish to secure.
Backup (Recommended):
Using the built-in backup function, you will export your keys to a location. That is secured using the encryption system.
Start Using Codes:
Retrieve the 6-digit code, or you can use the onetime passcode to sign in to multiple devices. And to verify your 2FA.
System Requirements
Operating System: The system should be running on Windows 10 or Windows 11 (64-bit).
Processor: Any Intel Core i3 or higher processor is recommended.
Memory: The memory should be 4 GB RAM or more.
Storage: For the program to run on the system smoothly. You would need only just 100 MB of free disk space.
Display: You should have at least a 1280×720 resolution or higher.
Network: n/a (Offline operation is supported)
Optional: Opt for the webcam (QR code scanning) if needed.
>>> Get Software Link…
Your File Password : 123
File Version & Size : 1.1.1 | 15 MB
File type : compressed / Zip & RAR (Use 7zip or WINRAR to unzip File)
Support OS : All Windows (32-64Bit)
Virus Status : 100% Safe Scanned By Avast Antivirus