Introduction
GhostVolt : Version 2.44.27 (Latest Software) is a complete solution for file safety, which includes up-to-date techniques of encryption and file sharing security that enhance and protect your data. In the era of the digital domain, where information leaks and cyberattacks have become a regular occurrence, GhostVolt is a major asset for both an individual and an organization, which has committed to privacy and information security.

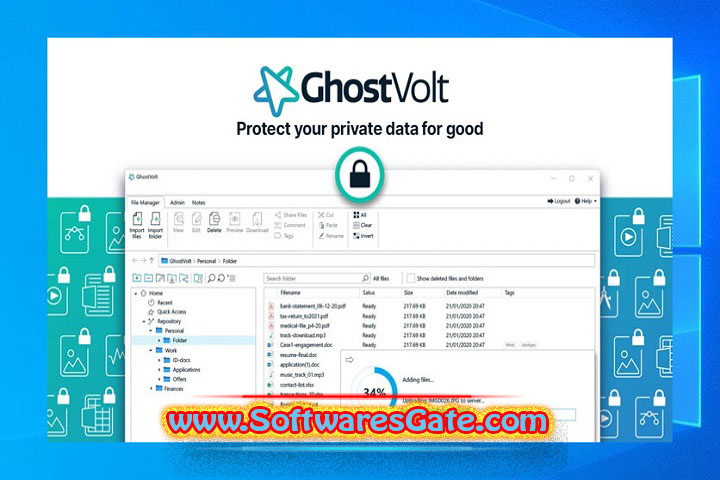
The online file security system provided by GhostVolt Ltd. allows users to generate confidential repositories (vaults) where confidential documents and folders that have securely kept can be put. This authorizes only the individuals with the particular credentials to access the documents, to modify or encrypt the list. To guarantee that your data will (omit)be seen and modified only by you, GhostVolt employs AES-256 encryption, whose strength remains unbeatable in terms of data protection control.
A more powerful 2.44.27 version of GhostVolt would present improved performance attributes, such as system management for multiple users, quicker encryption processing, and build services beyond this. A company working with client data or an individual maintaining personal files can trust GhostVolt and not worry about their security because it helps them to be in charge and in control of their own privacy.
You May Also Like :: Reuschtools ClassicMenu : Version 4.65 (Latest Software)
Description
GhostVolt 2.44.27 has tailored to ensure that end-to-end encryption has there to provide comprehensive file safety. It is a union of simplicity and top security that respects and supports the needs of both individuals and teams in protecting files and data with little or no knowledge of IT or security systems. It encrypts files automatically upon addition to the vault, which means your data is always well-secured, even if the files were copied or shared to go outside of the application.
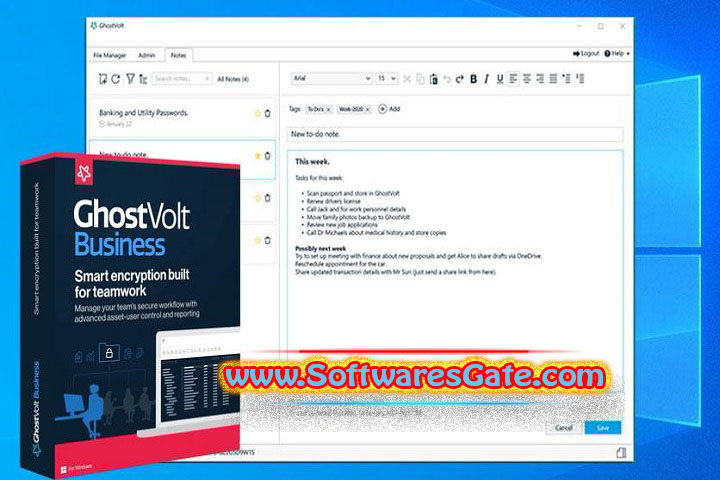
Through the team collaboration and access management features, GhostVolt is a representation of new-age ghost mode. A multi-user platform can be a dynamic environment, which is quite likely to have different access levels read; write; delete for the engineered purpose of the organization. Moreover, it has become very common in business to have several employees including sensitive information like client records, contracts, or financial data.
One of the main features of the GhostVolt program is its functionality for synchronized file sharing, in addition to data encryption. This is an exciting feature as well as a user-friendly feature that makes it simple to share files within a team without any hassle. Files to be crowded on the network have encrypted to ensure not only data leakage but that all actions have logged, for traceability and an audit trail.
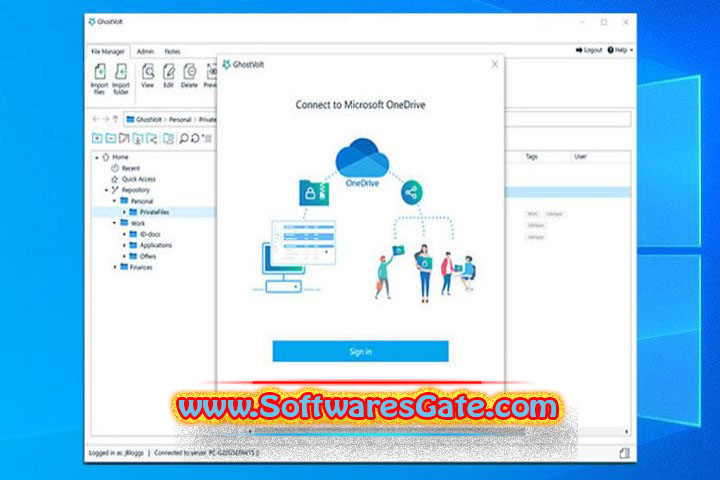
GhostVolt links with many cloud providers, such as OneDrive and Dropbox, to save your encrypted files on the cloud while fully keeping(omit) the local encryption keys. This means that regardless of whether your cloud account has hacked by someone else, your files can’t be read by unauthorized people.
GhostVolt 2.44.27 is not a mere encryption solution it functions as an all-around data security center that lets you create audit trails, enforce password policies, and set up automated backups. As part of the design, users will experience everything that would exist in a Windows File Explorer a very intuitive interface.
Overview
Built upon the core of GhostVolt 2.44.27, it offers a secure system of file management and team collaboration. Under the auspices of basic file locking or simplistic encryption utilities. GhostVolt provides a multi-level data security system (encryption, access control, and audit). Making longer chains of ransomware impossible.
When you register in GhostVolt, the process begins with a Vault creation. Representing where all of your encrypted files have stored. The encryption of each file put into the vault uses the AES-256 bit algorithm. Which has the most durable encryption. That has popularly acknowledged worldwide.
The vault can be kept at your location, on a network drive, or even combined. Making it possible for both individuals and teams. With the group usage in mind. The GhostVolt Business Edition has team collaboration features. Including the ability to create user accounts, permission roles, and management control.
The zero-knowledge encryption policy of GhostVolt ensures that it is only the user that has the keys/ data to decrypt your files – the developers and third parties don’t have access to your data. Thus, this hosting method is an almost perfect choice for all those users who consider paramount privacy and independence than cloud-account managed encryption.
The GUI of GhostVolt is very modern and user-friendly. With a file and workspace manager much the same as files today. The app comprises a feature that allows the user to pull the files to the vault. Either by a simple drag. And-drop action of the left mouse button or through the use of the menu item of Windows Explorer. The program also ensures that the data has protected by offering versioning options in addition. Which would enable data recovery from accidental deletes or corruption of the data.
The code in version 2.44.27 has better performance in handling the encryption/decryption process due to performance optimization. In addition, security updates were replayed as well to improve the software against recent threats mainly to get you with safer and efficient use in the system.
You May Also Like :: Chief Architect Premier X17 : Version v27.2.1.2 (Latest Software)
Software Features
Advanced AES-256 Encryption:
Top-tier 256-bit encryption prevents unauthorized access to activities. When taken or shared with others.
Secure File Vaults:
Formulate secluded data storage zones exclusively for keeping important. Or confidential documents that can be accessed by you alone.
User Access Control:
Management of access by users(omit) can be done through granting certain levels of clearance. For instance, some people can only view while others can allow editing.
<p>Team Collaboration Tools:
The secure sharing of encrypted files within your group network allows you to work together more effectively and efficiently without compromising privacy.
Cloud Integration:
Synchronize self-controlled storage with cloud services like OneDrive and Dropbox while retaining all your encryption keys.
Zero-Knowledge Security:
Only you, with your key, can read the encrypted files. The rest, from servers to other third-party processors, will all be at a loss.
Audit Logging:
Log all file changes, opening, edits, and deleting to have a complete history of actions. And to be able to produce reports as needed for the officials or as required.
Automated Backups:
Arrange periodic schedule times to secure vault content to mitigate. Data loss in extreme situations- systematic or humankind shortfalls.
File Versioning:
This keeps previous versions of your files in place to facilitate the undoing of changes. And to make easy data recovery.
Password and Authentication Management:
Hard and fast password rules as well as two-factor authentication. When not prohibited, enhance the top security of the documents, plans, or hands.
Software Features
Fast Encryption and Decryption:
Maximally optimized ciphers are responsible for handling files promptly and avoiding compromising the performance level.
File Search and Preview:
The files in the vault can be searched for fast location. And examination of the content without the manual deciphering that consumes time.
Secure Sharing:
Use secure transfer of encrypted files to avoid disclosing the data conducted through open channels.
Customizable Permissions:
Admins may set distinct group permissions- view only, edit by group members, or full control by team leaders.
Network and Multi-User Support:
Ideal for group projects with more substantial assignments has the fact. That it can be operated off shared drives, and the software permits multiple concurrent users.
Detailed Reporting:
Provide all customers with the material compliance documents, software use track, rating and analyzing about data quality.
Modern User Interface:
The design appears chic and stylish, mimicking the design featured in Windows Explorer, reducing to an absolute minimum the technology know-how one should have.
Regular Updates and Security Enhancements:
Choosing to update the software has the best option for supporting the latest threats that can easily be defended.
Data Integrity Protection:
Ensures that there remains no foul play, e.g., data tampering. Or alterations, in the case of actual data encryption or transmission.
Lightweight and Resource Efficient:
Trims the program down to the small amount of resources. That it no longer impedes with your system, which gives it an edge over client programs.
You May Also Like :: ChessBase : Version 18.15 (Latest Software)
How To Install?
<p>Download the Setup File:
Go to the (omit)product and do the downloading of the(omit) installer of version 2.44.27 from the official GhostVolt site.
Run the Installer:
Open the downloaded .exe File by pressing twice to summon the installation process.
Accept the License Agreement:
Read through carefully, then agree by clicking to move onwards.
Choose Installation Location:
Opt for the folder where all the program files have going to be installed. Or take the suggested default configuration with just a click of the Next button.
Install the Software:
Click the Install button and be patient until configuration is complete.
Launch GhostVolt:
Start the software by launching it from the Start menu. Or clicking on the program shortcut on the desktop.
Create Your Vault:
Design a security space and initiate construction of a digital vault. That doesn’t require any real building materials.
Set Password:
Opt for a strong password or pass phrase that will be used for the vault. Generate an encryption key, and remember to keep it secret.
Add Files and Folders:
Just drop and pour your files into the vault, and watch them lock up.
Optional Setup (Team Use):
Make the necessary changes to add member accounts, permissions. And restrictions only when you are using the business edition on multi-users.
System Requirements
With these requirements, an easy-running program or one that mostly works the way you want has promoted on your PC.
Operating System: Microsoft Windows 10 or Windows 11 (64-bit)
Processor: Intel Core i3 or seen in terms of performance, the equivalent (2.0 GHz or faster is good)
RAM: Bare minimum memory where the processor can recycle programs without much delay minimum 4 GB (8 GB recommended)
Hard disk space: take a good 300 MB other than what you will need will go into encrypted files
Display: Choose a 1024×768 screen or probably even higher resolution to see a clearer display
Network, team collaboration or cloud integration will require the creation or scope setting of this need
Administrator Rights: You can’t do that one without being an administrator yourself first- needed for smooth installation prior to configuration.
>>> Get Software Link…
<p>Your File Password : 123
File Version & Size : 2.44.27 | 23 MB
File type : compressed / Zip & RAR (Use 7zip or WINRAR to unzip File)
Support OS : All Windows (32-64Bit)
Virus Status : 100% Safe Scanned By Avast Antivirus





