Asterisk Password Spy : Version 13.0 (Latest Software)
Asterisk Password Spy 13.0
Introduction
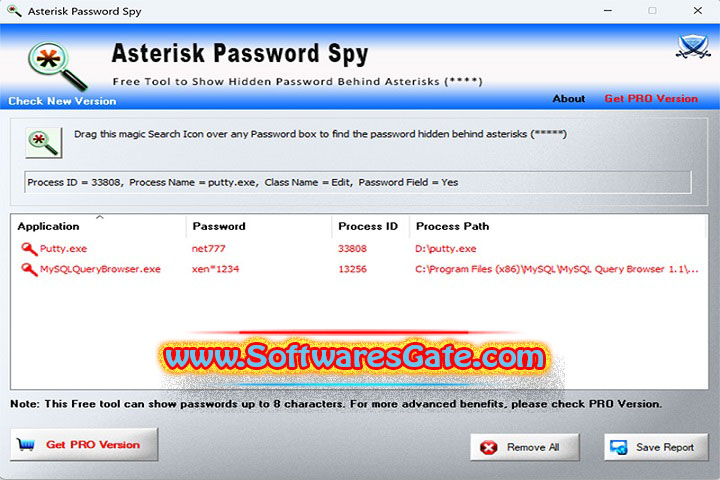
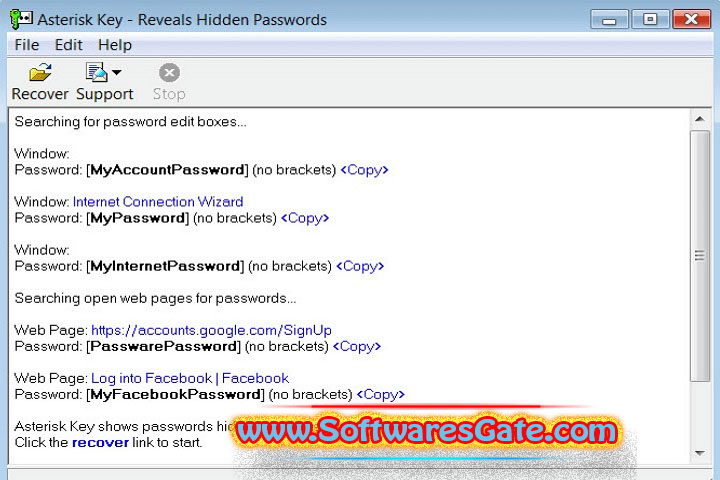
Asterisk Password Spy : Version 13.0 (Latest Software). Tools, which are trusted with exposing the hidden characters in the password fields something like the password reveal or the asterisk revealer apps often called do the job. These apps get the user’s attention easily because they offer a straightforward way to put the password that is lost (asterisk) in the pop-up dialogues or web forms that can be seen only as dots and one has to enter on another website. The release of version numbers such as “13.0” could suggest a product selection that is fully developed and updated for new features, as well as compatibility.

Even though there are situations where password retrieval from the user’s own machine could involve justified cause (for example, when a user may have spontaneously remembered a locally saved password but has no chance to recover the password through a password manager due to its own limitations), these tools can also be abused by hackers who have been trying to access other people’s credentials. Consequently, to make sure that the security is right, one has to analyze tasks, functional, legal, and responsibility-related items.
You May Also Like :: Arthouse Studio DWG to PDF Pro : Version 1.2.9 (Latest Software)
Description
The console password catcher application is a simple tiny desktop app that gets the job done by trying to ‘snatch’ password characters embedded in desktop applications or through the older web dialogs that are in use in common (where password is originally marked with ‘*’ or ‘•’).
Technically speaking, these utilities perform their function by reading the memory-mapped contents, understanding the fundamental core string, and ultimately displaying it on the interface. Today’s applications and web browsers practically apply secure methods (symmetric and asymmetric encryption, protected storing of login details, keychain integration, and temper-resistant systems), so that many disparate ways of accessing a program’s credentials no longer work the way they should.
Normally, legit vendors have a rather restricted usage for their tools (psychological and social password recovery) and include such warnings as using the tool only for personal recovery tasks. Praiseworthy companies, for instance, would stress (omit)consent, local on-premise deployments, and would not recommend for remote or stealth operations.
Overview
Misuse of password recovery tools has often possible if they are used to:
Give the user the ability to regain a password that had originally saved in a local application and may soon be out of reach to the user because the previous recovery strategies would not be available.
Bestow the IT technician with a detection and analysis tool, which works within the authorized support assistants sessions framework. Creation of security flaws as part of the advocacy for the implementation of better password processing habits as an effective approach to faster password gaining.
Due to the complications, many password recovery solutions are cascades. They incline towards OS keychains, password managers, and multi-factor authentication (MFA). This makes just-in-time password recovery practice quite ineffective in the ecosystem. Most current programs detour from storing passwords in their relocation; however, browsers such as IE and Edge store saved passwords in an encrypted vault, which has only allowed to use after unlocking the whole system.
You May Also Like :: Approximatrix Simply Fortran : Version 3.41.4435 (Latest Software)
Software Features
In the instance where the tool has been updated to the most current release, say like the 13.0, the selling point has likely to include specific aspects such as the following (note: these are high-level descriptions, not instructions):
Local Password Reveal Apparatus: Individual tries to probe within the local GUI of the operating system to recover the masked password fields.
Compatibility List: Adds compatibility for desktop applications in use before (portions of dialog text already stored in memory in retrievable form).
Built-in Legal/Ethical Warnings: These pre-programmed legal/ethical prompts point in case. And imply that the software has meant for legal use only.
No Remote Operation: While preferring local executions, there are no hidden remote collection events to avoid the risk of abuse.
Multiple Windows/Controls Detection: Functional UI supportive for all window controls that are in line with versions of Windows applications.
Unlike vendors who “assign” the configuration of Féas to respect pre-built libraries. And guards, fair vendors developed an option to adjust this by using “Custom Deployment Parameters.” Additionally, they make the first choice button “Run” more exposed in hopes of inciting a user pickup. Let us analyze whether the new testing paradigm clarified any issues with SecureDrop.
Logging Controls: Can choose to contribute to disabling logs. Or to just log actions on consent of the customer with the administrator’s approval.
Built-in Protection for OS Architecture Becomes Obsolete: When OS security has revised, the newest software releases have modified accordingly. In the process of enhancing the systems’ security and upgrade. Newer versions of software include the reduction of functionalities that allow for credential protection.
You May Also Like :: Alphabix : Version 4.1.1.0 (Latest Software)
Legitimate Use Scenarios and Applying Law/Ethics Data
Legitimate scenarios would entail a user’s password being recovered if there have no other means of recovery. Or an IT technician who has authorized retrieving such credentials during a support session. Upon implementing any tool like this:
Harvest explicit permission from the device owner first or, should you not document the provided authority. Always refer back to corporately established policies, or any existing signed authority
Basic data types should always be segregated from datasets with sensitive data. Such as information of a financial or health nature. And ensure that the policy has strict guidance that approves respective recovery measures
It is acceptable for you to choose to keep your passwords in a more secure location other. Than the OS password managers, which gives you that portability. Browser password export, which often requires you to unlock the system to allow for data import.. Or dedicated recovery systems are other safer alternatives available.
Cognize manipulating legal risk. Truly so, using these apps to break into someone’s email or other account violates privacy laws and. In many cases, falls short of the computer misuse statutes.
As one follows this process, one needs to maintain a private key to ensure the monetary details do not get exposed. Users can simply download software from the Tor Project’s official website. Opening this website alone will not subject you to scrutiny. So it is important to do so from a different machine.
It has advised that a party should only do business with those vendors. Who can provide a digital signature document to prove their authenticity. A monitored environment needs to be created to isolate the intrusions and to control them. This describes the “Sandbox” environment before the actual launch. GL.
How the system of this software functions: Rather than considering the central process. The provided information is on the tasks which allow the misuse of this guidance.

System Requirements
An up-to-date software implementation aimed at Windows desktop settings will most likely mention the necessity of a certain series of somewhat lenient parts’ specifications. These include the following statements:
Portal Items: Operating System: Windows 7, 8.1, 10, or 11 (even 64 bit for optimization)
Tool: Dual-core CPU or greater
Requisite Foundation: RAM: 2 to 4 gigabytes as a lower limit, but 4 GB or more has preferred
Hard disk requirements: tiny installation footprint (in the tens two hundreds of megabytes)
Privilege: Some operations and clicking on operations with a component (a pop-up or alike) may request the administrator mode (a need for authentication may occur)
>>> Get Software Link…
Your File Password : 123
File Version & Size : 13.0 | 9 MB
File type : compressed / Zip & RAR (Use 7zip or WINRAR to unzip File)
Support OS : All Windows (32-64Bit)
Virus Status : 100% Safe Scanned By Avast Antivirus